Who Else Wants Tips About How To Prevent Sql Code Injection Attacks

All user input must be filtered by websites.
How to prevent sql code injection attacks. 8 useful tips for how to prevent sql injection attacks. It is used to insert, update, delete, and search. In php, we are use mysql_real_escape_string() function to prevent this along with other techniques but.
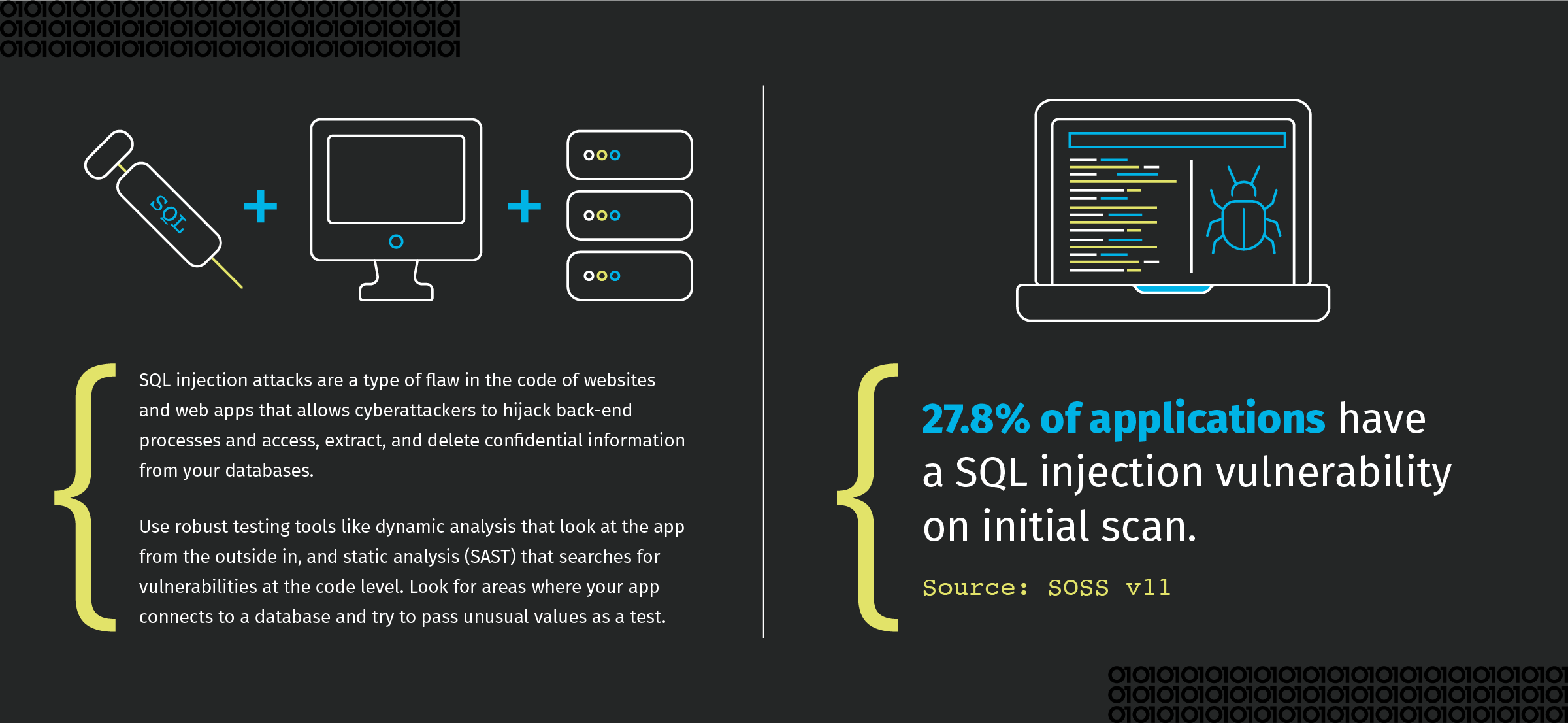
Types of sql injection attacks. Here are seven tips to help you prevent sql injection attacks. It is one of the standard languages to deal with the relational database.
What can be done to prevent sql injection attacks? This way, if one of your. It is used to insert, update, delete, and search the records stored in a.
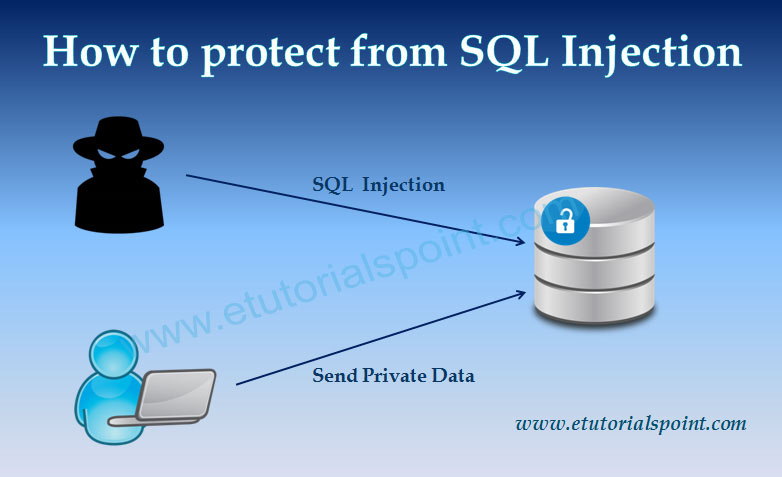
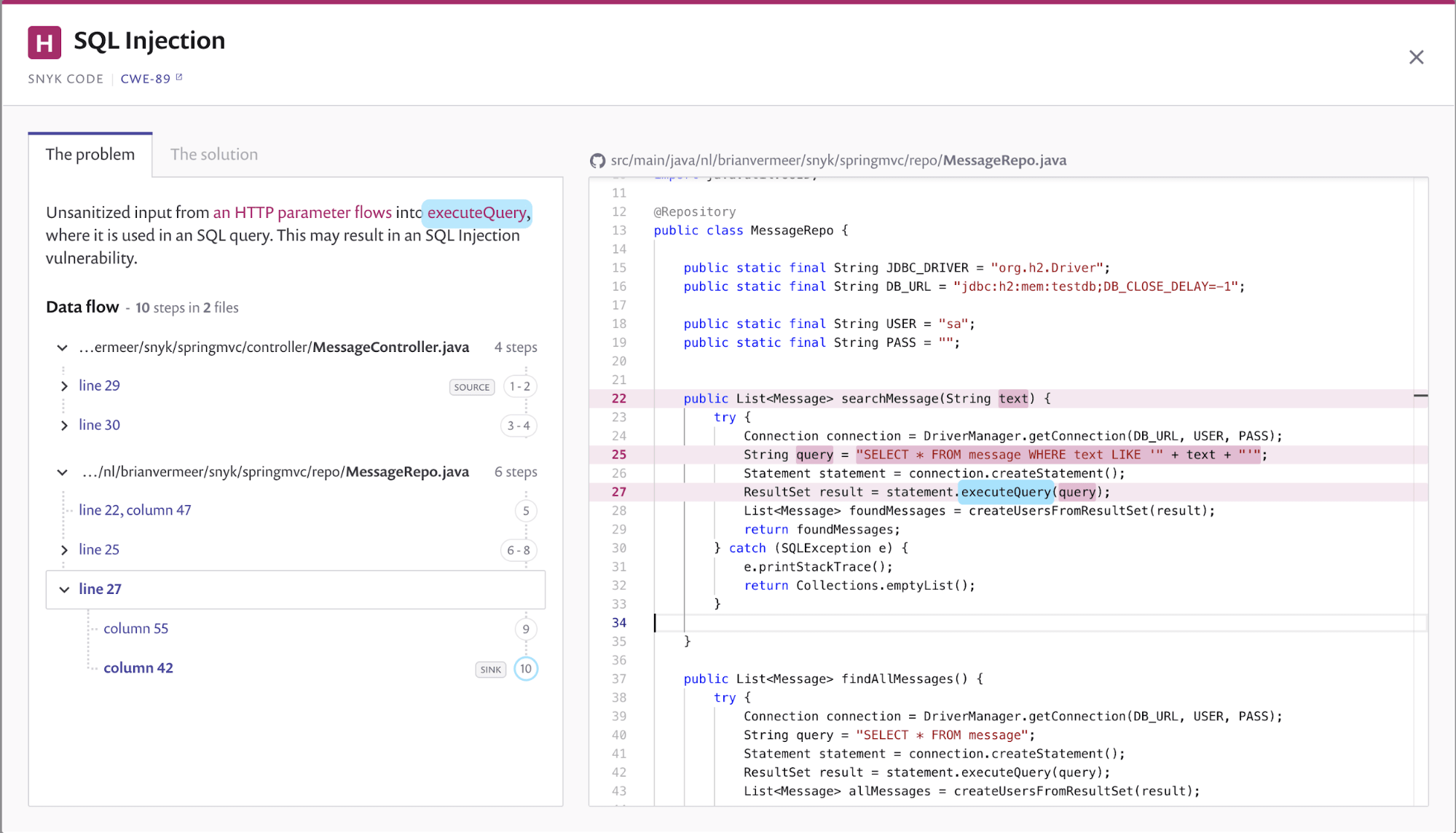
To reduce the risk of being a victim of a sql injection attack, take these steps: To prevent injection attacks on your web application, you must securely code them. Developers can prevent sql injection with the help of the following techniques.
The fromsql and fromsqlinterpolated methods are safe against sql injection, and always integrate parameter. In order to prevent sql injection attack, validating user inputs is a. In this attacks, the attacker inserts.
However, the standard sql commands such as “select”, “insert”, “update”, “delete”, “create”, and “drop” can be used to accomplish almost everything that one needs to do with a. Coordinate an investigation of potentially vulnerable web pages and resources amongst developers or other stakeholders. Connect and share knowledge within a single location that is structured and easy to search.
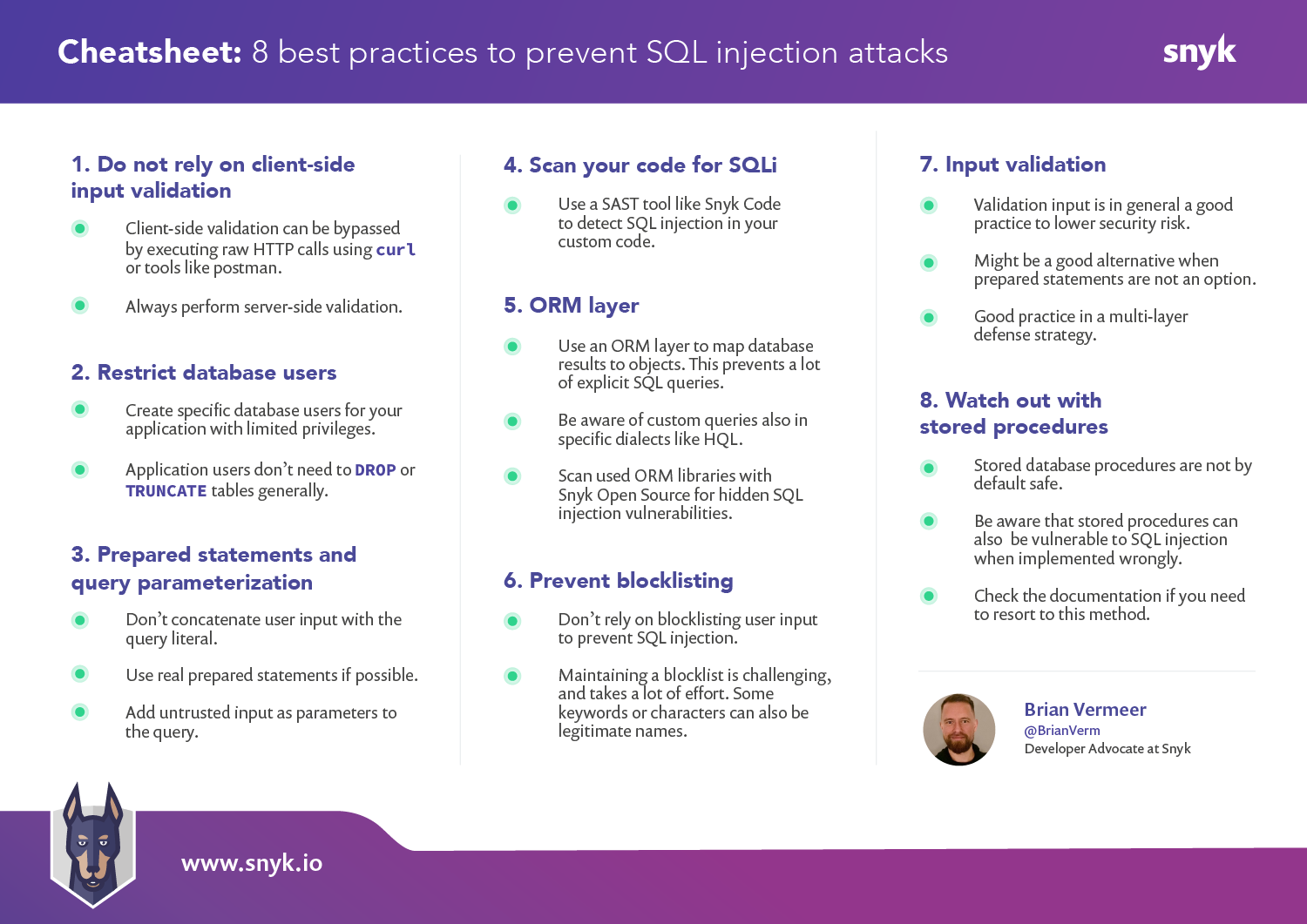
8 best practices to prevent sql injection attacks 1. Hackers don’t attack databases manually. Preventing sql injection in java code the simplest solution is to use preparedstatement instead of statement to execute the query.
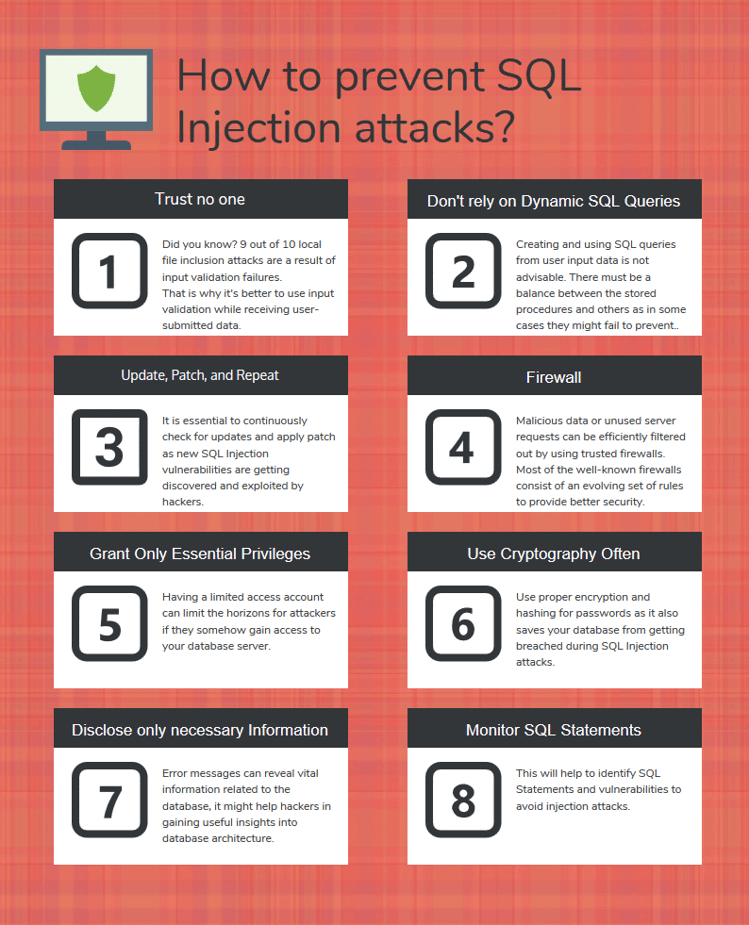
Using sqli to authenticate as administrator. Owasp has defined several ways to prevent sql. There are a few common ways to prevent sql injection attacks:
Don’t allow multiple statements use placeholders instead of variable interpolation validate user input. 1) continuous scanning and penetration testing 2) restrict privileges 3) use query parameters 4) instant protection what are. A review of web, application, and database logs may reveal.
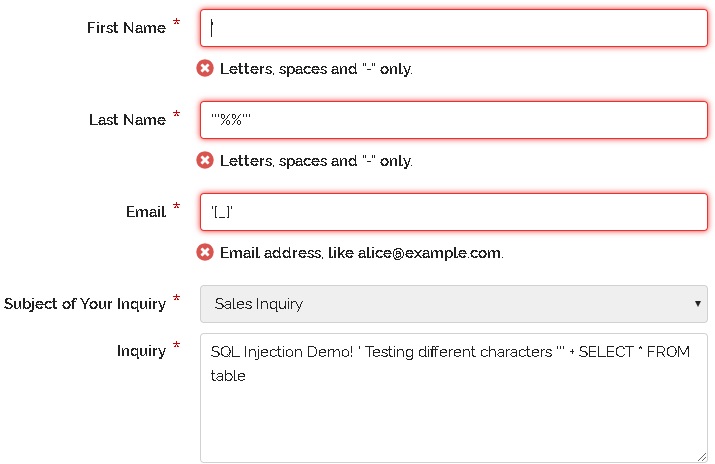
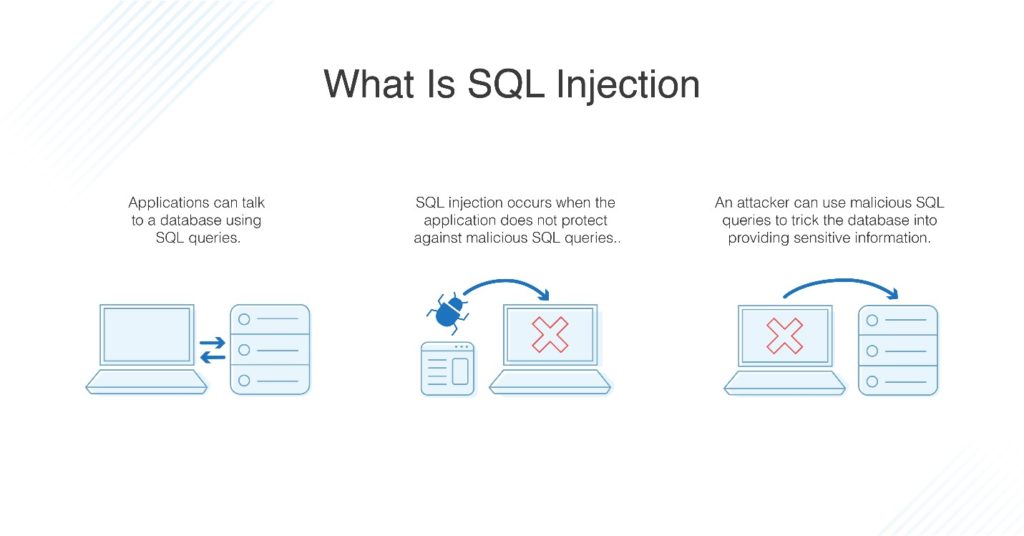
The most important precautions are data sanitization and validation, which should already be in place. Structured query language is the full form of sql. Sql injection is an attack made on database query.